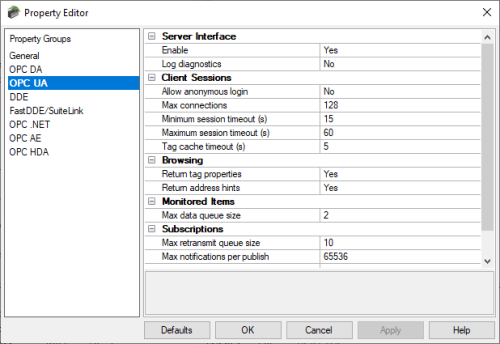
Comprehensive management for OPC UA endpoints and security settings
The TOP Server OPC UA Configuration Manager is accessible through the TOP Server Administration system tray icon and provides centralized management of all OPC UA server endpoints, their associated ports and supported security and encryption settings and management for trust relationships with OPC UA servers and clients.
The OPC UA Configuration Manager is also key to managing secure certificates whether you're self-issuing an OPC UA certificate or importing a certificate from a third-party firm.